Awareness and Security is dedicated to cybersecurity education, online privacy, and digital protection. Discover security tips, threat analysis, hacking awareness, account protection methods, and practical guides designed to help users stay safe in the modern digital world.

- Details
- Written by: khalil shreateh
- Category: Awareness and Security
- Hits: 123
Introduction: The Price of Living in a Connected World
The digital age has transformed almost every aspect of modern life. We bank online, communicate through messaging apps, store our most sensitive documents in the cloud, and connect dozens of devices to home networks without giving it much thought. The convenience is extraordinary. But so is the risk.
Every device you connect to the internet is a potential entry point. Every account you create is a credential that can be stolen. Every network you join without checking is a conversation that could be overheard. Cybercriminals are not the shadowy lone hackers of Hollywood films — they are organized, well-funded, and methodical, operating on a global scale and targeting individuals, businesses, hospitals, and governments with equal enthusiasm.
Understanding the threats is the first and most important step in defending against them. You cannot protect yourself from something you do not recognize. This guide breaks down the most prevalent cybersecurity threats in plain language, illustrates each with real-world examples, and walks you through the concrete steps you can take to significantly reduce your exposure.
Read more: Security Threats: Fortifying Your Defense in the Digital World

- Details
- Written by: khalil shreateh
- Category: Awareness and Security
- Hits: 190
Why Your Online Privacy Is Worth Protecting Right Now
Every time you sign up for a website, you hand over a piece of your identity. It might feel harmless — just an email address here, a name there — but the reality of what happens to that data after you click the register button is something most people never think about. The website stores your information in a database. That database may be sold to advertising companies, leaked in a data breach, or mined by third-party data brokers who build detailed profiles about millions of people and sell them to whoever is willing to pay.
The result, at its mildest, is a flooded inbox full of spam newsletters you never asked for. At its worst, your real name, email address, and browsing habits are circulating in marketing networks and potentially in places far less reputable. The fact that this is technically legal in many jurisdictions does not make it any less of a problem for ordinary users who just wanted to download a file or read one article.

- Details
- Written by: khalil shreateh
- Category: Awareness and Security
- Hits: 15202
Facebook Account Security
By Khalil Shreateh — Information Security
Are you aware that your account could be at risk?
Many people have had their accounts hacked. If it has happened to you, or you know someone it happened to, you are not alone. From phishing pages that steal your login credentials, to malware files (.exe) distributed through games, chat apps, and social networks — the threats are real and varied.
Be cautious of links sent to you that claim to contain something important. Be especially careful if a link asks you to log in again — check whether the website address is actually facebook.com and not something like (facebook . hosting2 . com).

- Details
- Written by: khalil shreateh
- Category: Awareness and Security
- Hits: 108
The digital landscape has shifted from an era of optional encryption to one where secure origins are the non-negotiable foundation of the web platform. This transition is not merely a cosmetic change or a push for a "green lock" icon in the address bar; it is a fundamental response to the increasing sophistication of man-in-the-middle (MiTM) attacks, data interception, and the rise of powerful web APIs. As we integrate features like Service Workers, Push Notifications, and Geolocation into the fabric of our applications, the surface area for potential exploits expands. Consequently, the browser has evolved from a simple document viewer into a complex security enforcement engine.
Read more: Securing the Modern Web: An In-Depth Look at the Chrome DevTools Security Panel
- Details
- Written by: khalil shreateh
- Category: Awareness and Security
- Hits: 102
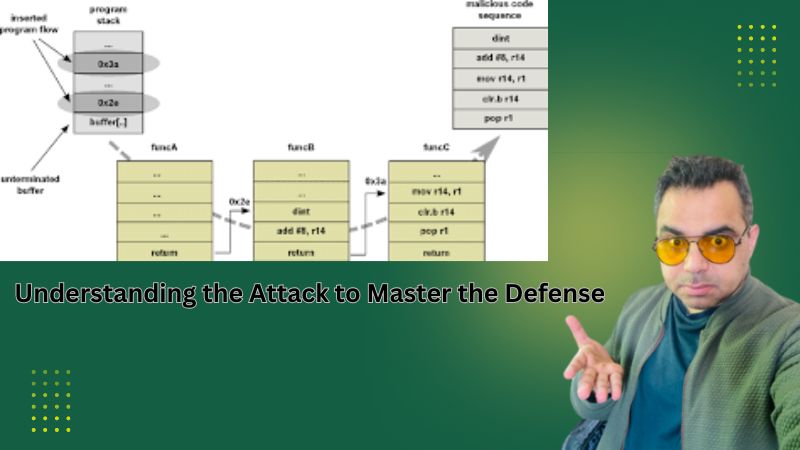
A Defender-Oriented Deep Dive into Memory Exploitation and Modern Mitigations
Return-Oriented Programming (ROP) is one of the most sophisticated and enduring code-reuse exploitation techniques in modern cybersecurity. First formalized in academic research in the mid-2000s, ROP enables attackers to execute arbitrary logic on a target system without injecting a single byte of new code. Instead, they chain together small sequences of pre-existing instructions already present in the application's own binary or its linked libraries — making the attack invisible to memory protections that only ask whether a page is executable.
Read more: Return-Oriented Programming: Understanding the Attack to Master the Defense
- SQL Injection, Defensive Strategies & OWASP Guidelines
- Network Security Bible: A Comprehensive Cybersecurity Awareness and Research Guide
- Network and System Security: A Comprehensive Cybersecurity Awareness and Research Guide
- Understanding Error-Based SQL Injection in ASP/ASPX Applications: A Security Awareness Guide