Why ASP and ASPX Applications Remain High-Value Targets
Web applications built on Microsoft's ASP and ASP.NET (ASPX) frameworks have powered some of the world's most widely deployed enterprise and public-facing systems for decades. Despite advances in secure development tooling and growing awareness of application security, SQL injection remains one of the most consistently exploited vulnerability classes in this ecosystem. Understanding precisely how these attacks work — from the attacker's perspective — is not an endorsement of malicious activity. It is the foundation of effective defense. Security professionals, developers, and system administrators who understand the mechanics of exploitation are far better positioned to build and maintain systems that resist it.
This article examines the methodology behind manual, error-based SQL injection attacks targeting ASP/ASPX applications, explains why the Microsoft SQL Server error reporting mechanism is so frequently abused in this context, and outlines the defensive controls that make such attacks impossible to execute successfully.
What Is Error-Based SQL Injection?
SQL injection is a class of vulnerability in which an attacker is able to insert or manipulate SQL query logic by supplying crafted input through an application's user-facing interface. When that input reaches a database query without proper sanitization or parameterization, the database interprets the attacker's payload as legitimate query syntax.
Error-based SQL injection is a specific variant that exploits the application's own error reporting to extract information directly from the database. Rather than relying on inferential techniques — such as observing whether a page loads differently based on a true or false condition — error-based injection deliberately causes the database to generate a meaningful error message containing the data the attacker seeks to retrieve. In Microsoft SQL Server environments, which underpin most ASP/ASPX applications, this is made possible by the behavior of type-conversion functions such as CONVERT() and CAST(). When these functions are asked to convert a text string — such as a database name, table name, or stored password — into an incompatible data type such as integer, SQL Server raises a conversion error that includes the original string value in its message. The attacker reads that value directly from the error output displayed by the application.
This technique is particularly effective against applications that expose verbose error messages to end users — a common misconfiguration in development environments that frequently persists into production deployments.
How Attackers Identify Vulnerable ASP/ASPX Endpoints
The first step in any SQL injection assessment, whether conducted by a legitimate penetration tester or a malicious actor, is identifying an injection point. In ASP/ASPX applications, these are most commonly found in URL query string parameters that pass user-supplied values directly into database queries. A URL of the form index.aspx?id=10 or search.aspx?txt=EDIT is a classic indicator that the parameter value may be concatenated into a SQL query on the server side.
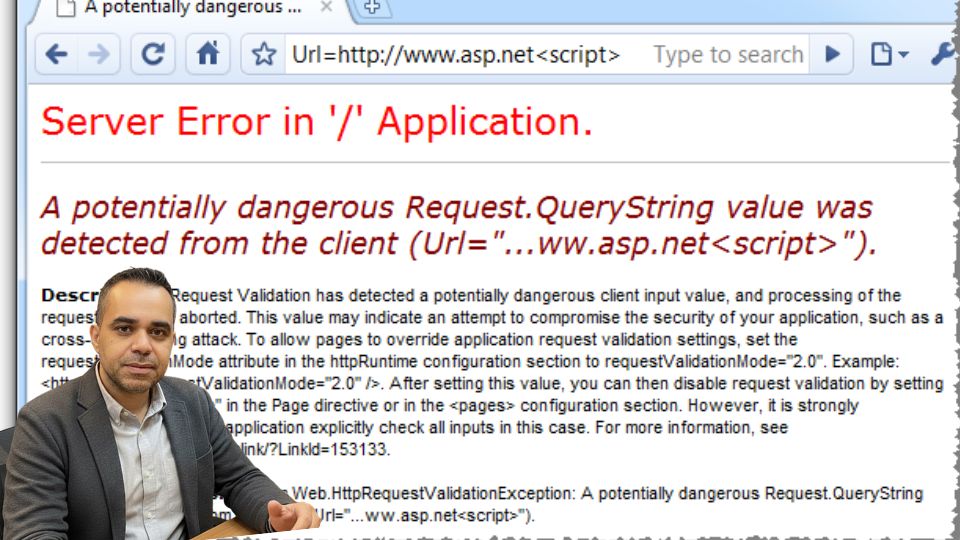
The most elementary test for injection vulnerability is the single-quote probe. By appending a single apostrophe character to the parameter value in the URL, an attacker submits syntactically malformed SQL to the server. If the application lacks proper input handling, the malformed query reaches the database engine, which raises a syntax error. When the application propagates that error to the browser — displaying a message such as "Unclosed quotation mark after the character string" or "Incorrect syntax near" — it simultaneously confirms the injection point and reveals that the application exposes raw database error messages. Both of these facts are highly valuable to an attacker.
A secondary confirmation step involves appending a HAVING 1=1-- clause to the parameter. If the underlying query uses a GROUP BY construct, this produces a different and more informative error message — specifically one that reveals an actual column name from the database query, further confirming exploitability and beginning the process of schema enumeration.
Enumerating the Database: Server Version, Name, and User
Once an injection point is confirmed, an attacker using the error-based technique can immediately begin extracting foundational information about the database environment. By injecting AND 1=CONVERT(int,@@version)-- into the vulnerable parameter, the attacker forces SQL Server to attempt to convert its own internal version string into an integer. The conversion fails — as it must, since the version string is text — and SQL Server helpfully includes the full version string in the error message. This reveals the precise SQL Server version, edition, and operating system, which informs the attacker about which further techniques and exploits may apply.
The same mechanism is used to retrieve the database name via db_name() and the currently connected database user via user_name(). These two pieces of information are operationally significant: the database name scopes subsequent queries, and the database user's privilege level determines how far the attack can be extended. A connection running as dbo or sa — common misconfigurations — gives an attacker substantially broader access than a minimally privileged application account.
Enumerating Tables Through the Information Schema
With the database name and user context established, the attacker proceeds to map the database schema. Microsoft SQL Server, like all ANSI-compliant relational database systems, exposes metadata about its structure through a set of system views collectively known as the information schema. The information_schema.tables view contains a row for every table in the current database, including the table's name.
By injecting a subquery that selects the top result from this view and forcing a type-conversion error, the attacker retrieves the first table name from the error message. To retrieve subsequent table names, the attacker iterates using a NOT IN exclusion clause — each successive query adds the previously discovered table name to an exclusion list, causing SQL Server to return the next table in sequence. This process continues until the attacker identifies a table whose name suggests it holds administrative credentials, user accounts, or other sensitive data. Names such as admin, users, members, or prefixed equivalents are the primary targets.
Enumerating Columns Within Target Tables
Once a table of interest is identified, the attacker applies the same iterative approach to enumerate its column structure, this time querying the information_schema.columns view with a filter on the target table name. The first query returns the first column name embedded in a conversion error. Subsequent queries exclude previously discovered column names until the attacker has a complete list of all columns in the table. In a typical attack against an administrative credential table, the target columns are those holding email addresses or usernames and plaintext or hashed passwords.
The fact that neither column count discovery nor UNION-based techniques are required in this approach is a meaningful distinction from the more commonly documented PHP/MySQL injection methodology. Error-based injection against SQL Server allows direct schema traversal without the intermediate steps of determining column counts or identifying injectable columns in a SELECT statement — making it a relatively efficient attack path when error messages are exposed.
Extracting Data: Credentials and Beyond
With the target table and column names in hand, the final phase is data extraction. The attacker constructs subqueries that select actual data values — email addresses, usernames, passwords — from the target table and embeds them in the same CONVERT(int, ...) pattern used throughout. SQL Server's conversion error faithfully returns each value in the error message. By iterating with NOT IN exclusion clauses, the attacker can extract every row in the table sequentially.
The implications are severe. If the extracted passwords are stored in plaintext, immediate access is possible. If they are hashed, the attacker takes the hashes offline for cracking attempts using widely available tools and wordlists. Either way, the result is a full compromise of the administrative credential store — and often a pathway to complete application takeover.
Why This Attack Succeeds: The Root Causes
Understanding the conditions that enable error-based SQL injection is essential for prevention. Three root causes are responsible for the vast majority of successful attacks in this category.
The first and most fundamental is the absence of parameterized queries or prepared statements. When application code constructs SQL queries by concatenating user-supplied input directly into query strings, any input validation can be bypassed and any SQL syntax can be injected. Parameterized queries eliminate this risk entirely by separating query structure from data values; the database engine never interprets user input as SQL syntax, regardless of its content.
The second root cause is the exposure of verbose database error messages to end users. SQL Server's type-conversion errors are informative by design — they are intended to help developers diagnose data type mismatches during development. When an application propagates these messages to production users verbatim, it transforms a debugging aid into an intelligence-gathering tool for attackers. Properly configured production applications should display generic, user-friendly error messages while logging detailed error information server-side for legitimate diagnostic purposes.
The third contributing factor is the use of overly privileged database accounts for application connectivity. When an application connects to its database using an account with administrative or database-owner privileges, a successful SQL injection attack inherits those privileges. Minimally privileged application accounts — restricted to the specific SELECT, INSERT, UPDATE, and DELETE operations the application legitimately requires — contain the blast radius of any injection vulnerability that may exist.
Defensive Controls: Building Applications That Resist This Attack
The security controls required to prevent error-based SQL injection attacks are well-established, well-documented, and entirely within the reach of any development team.
Parameterized Queries and Stored Procedures
The single most effective control against SQL injection of all types is the consistent use of parameterized queries, also known as prepared statements. In ASP.NET applications, this means using SqlCommand objects with SqlParameter collections rather than string concatenation to build queries. Stored procedures can also provide a clean separation between query logic and data, provided they internally use parameterized input rather than dynamic SQL construction. This control alone renders error-based injection — and indeed most SQL injection techniques — non-functional at the point of data access.
Suppressing Verbose Error Messages in Production
All ASP.NET applications should be configured with customErrors mode set to On or RemoteOnly in the web.config file, ensuring that detailed exception information, including stack traces and SQL error messages, is never transmitted to browser clients in production environments. Custom error pages should provide helpful navigation for legitimate users while revealing nothing about the underlying technology stack, query structure, or database schema. Detailed error information should be captured through structured server-side logging — such as Windows Event Log entries or Application Insights telemetry — accessible only to authorized operations personnel.
Principle of Least Privilege for Database Accounts
Every ASP/ASPX application should connect to its database using a dedicated, minimally privileged service account. This account should be granted only the permissions required for the application's legitimate operations — typically SELECT on specific tables and EXECUTE on specific stored procedures — and nothing more. It should never have access to information_schema views, system catalog tables, or administrative functions. While this control does not prevent injection, it dramatically limits what an attacker can accomplish if an injection vulnerability is discovered, because the injected queries run under the same restricted privileges as the application itself.
Input Validation as a Defense-in-Depth Layer
While parameterized queries are the primary defense against SQL injection, input validation provides an additional layer of protection. All user-supplied input should be validated against a strict whitelist of expected characters, formats, and value ranges before it reaches any processing logic. Numeric ID parameters should be validated as integers. Search strings should be constrained to expected character sets. Inputs that fail validation should be rejected with an appropriate HTTP response, not passed downstream to query logic. This defense-in-depth approach ensures that even if a parameterized query is inadvertently omitted somewhere in the codebase, the input validation layer provides a secondary barrier.
Web Application Firewalls and Security Testing
A properly configured Web Application Firewall (WAF) can detect and block SQL injection payloads in HTTP requests, providing an additional layer of protection at the network perimeter. However, a WAF is a compensating control, not a substitute for secure coding practices. Attackers routinely devise obfuscation techniques to bypass WAF rule sets, and a WAF provides no protection against injection that occurs through application logic rather than HTTP parameters.
Regular security testing — including automated dynamic application security testing (DAST) and manual penetration testing by qualified professionals — is essential for identifying injection vulnerabilities before attackers do. All SQL injection findings, regardless of severity classification, should be remediated promptly and verified through retesting.
The Responsibility of Developers and Organizations
The techniques described in this article are not sophisticated. They require no specialized tools, no exploit frameworks, and no advanced programming knowledge. They require only a browser and an understanding of SQL Server's error reporting behavior. This accessibility is precisely what makes the vulnerability class so persistently dangerous: the barrier to exploitation is low, while the impact of a successful attack can be catastrophic.
Every developer who writes code that touches a database has a responsibility to understand how SQL injection works and to apply parameterized queries by default. Every organization that deploys web applications has a responsibility to test those applications for injection vulnerabilities, to suppress verbose error messages in production, and to enforce the principle of least privilege throughout their data access architecture. These are not aspirational security goals — they are baseline engineering standards.
- Error-based SQL injection against ASP/ASPX applications exploits a straightforward combination of missing input parameterization and excessive error verbosity to enumerate entire database schemas and extract sensitive data through the application's own error messages. The attack methodology is iterative, manual, and highly effective against misconfigured systems. The defensive controls that neutralize it — parameterized queries, suppressed error output, least-privilege database accounts, and regular security testing — are mature, well-understood, and universally applicable. Closing this gap is not a question of technical complexity. It is a question of disciplined engineering and organizational commitment to secure development practice.
Written by Khalil Shreateh Cybersecurity Researcher & Social Media Expert Official Website: khalil-shreateh.com