What Is Cross-Site Scripting (XSS)?
Cross-Site Scripting, commonly known as XSS, is one of the most prevalent and dangerous vulnerabilities in modern web applications. It occurs when untrusted user data is processed by a web application without proper validation and is then reflected back to the browser without encoding or escaping. The result is unintended code execution within the user's browser — a foothold that attackers can exploit to steal session cookies, redirect users, deface interfaces, or launch further attacks.
Understanding XSS is not merely an academic exercise. It is a foundational requirement for any developer responsible for building or maintaining web-facing applications.
Types of XSS Attacks
XSS is not a single, monolithic attack. It manifests in several distinct forms, each with its own attack vector and risk profile.
Reflected or Non-Persistent XSS
In this variant, the attacker's malicious input is immediately processed by the server without validation and reflected back in the HTTP response without encoding. The attack is typically delivered through a crafted URL. Because the payload is not stored, it requires the victim to actively click the malicious link — but the consequences can be severe nonetheless.
Stored or Persistent XSS
Stored XSS is considered the most dangerous form. Here, the attacker's payload is saved in the application's backend — a database or file — without sanitization. Every time the affected data is retrieved and rendered, the malicious script executes in the victim's browser. Unlike reflected XSS, no interaction with a crafted link is needed after the initial injection.
DOM-Based XSS
DOM-based XSS is a client-side vulnerability. Both the source and sink of the malicious data reside entirely within the browser's Document Object Model. The data flow never leaves the browser, yet the attack succeeds when untrusted data manipulates the DOM environment in a way that triggers script execution. Traditional server-side defenses alone are insufficient here.
Mutation XSS (mXSS)
Mutation XSS is perhaps the most insidious variant. A payload that appears completely harmless — and may even pass through client-side or server-side XSS filters — gets mutated by the browser's HTML rendering engine when processed via the innerHTML property, transforming into a valid attack vector. XSS filters alone cannot prevent mXSS. Effective mitigation requires a well-configured Content Security Policy, prevention of framing, and strict DOCTYPE declarations.
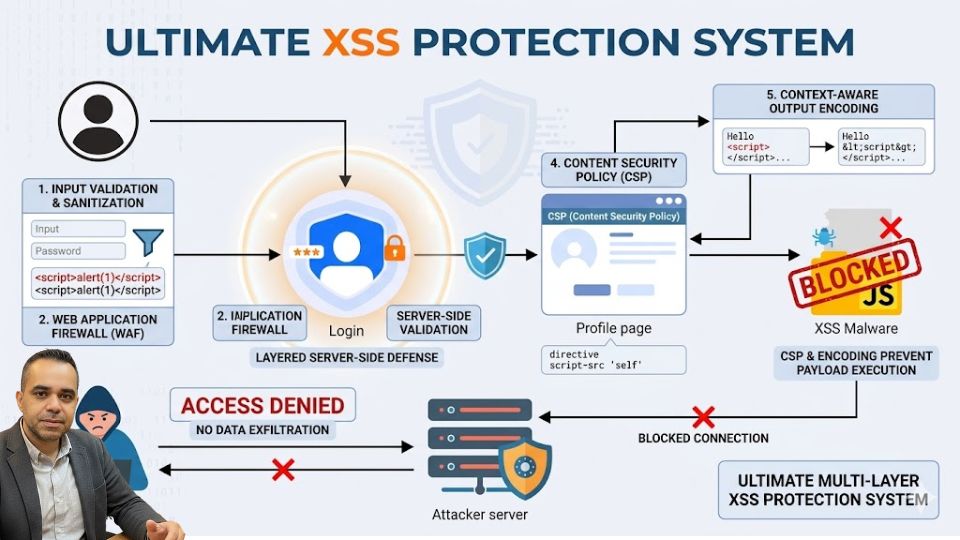
The Core Principles of XSS Protection
Preventing XSS requires a layered, defense-in-depth approach. No single technique is sufficient on its own. The following principles form the backbone of any robust XSS defense strategy.
Validate Input and Escape Output Based on Context
The most fundamental rule is to treat all user-supplied data as untrusted. Every piece of data that originates outside the application — from form fields, URL parameters, HTTP headers, cookies, or APIs — must be validated before processing and escaped before being reflected in any response.
Critically, the type of escaping required depends entirely on the context in which the data will appear. The browser parses content in a specific order: first the HTML parser, then the CSS parser, and finally the JavaScript parser. The decoding order follows the same sequence. Applying the wrong encoding, or applying it in the wrong order, can introduce new vulnerabilities even when the developer believes the data is safe.
Escaping in the HTML Context
When untrusted data appears within standard HTML body content, HTML entity encoding must be applied. Characters such as &, <, >, ", ', `, and / must be converted to their corresponding HTML entities.
Escaping in the HTML Attribute Context
When untrusted data is inserted into an HTML attribute value, HTML escaping must be applied and the attribute value must always be enclosed in quotes — either single or double. Backticks must never be used as attribute delimiters. All characters with ASCII values below 256 (except alphanumerics) should be escaped to prevent attribute breakout.
Escaping in JavaScript and Event Handler Contexts
For data embedded within JavaScript strings or event handler attributes, JavaScript string escaping must be applied first. When data appears inside an event handler attribute (which is parsed by both the HTML and JavaScript parsers), JavaScript escaping must be performed first, followed by HTML escaping — because the browser decodes HTML attributes before processing JavaScript.
Escaping in URL Contexts
Untrusted data embedded in URL parameters must be URL-encoded. Crucially, only the path or parameter value should be encoded — never the entire URL. The href and src attributes must never accept javascript: or data: URI schemes, including obfuscated variations.
Escaping in CSS Contexts
When untrusted data appears within a CSS property value or a style attribute, CSS string escaping must be applied first, followed by HTML escaping (since the HTML parser runs before the CSS parser). Strings must be quoted, and dangerous CSS expressions — including obfuscated variants — must be explicitly blocked.
HTML in JavaScript Strings
When rendering HTML within a JavaScript string (for example, setting innerHTML), HTML escaping must be applied first, then JavaScript string escaping. This order is critical and must not be reversed.
Always Prefer Whitelists Over Blacklists
A blacklist approach — attempting to block specific known-malicious inputs — is inherently fragile. Attackers routinely devise novel payloads that bypass filters. A whitelist approach, where only explicitly permitted tags, attributes, and characters are allowed, is far more robust and should be the default strategy for input validation and output sanitization.
Use UTF-8 as the Default Character Encoding
All HTML documents should declare UTF-8 as their character set using the appropriate <meta> tag. No user-controlled content should appear before this meta tag in the document, as injections placed before the charset declaration can override it and introduce alternative character sets capable of enabling XSS vectors.
Always Declare a DOCTYPE
The <!DOCTYPE html> declaration instructs the browser to parse and render the document according to a defined standard. Without it, browsers may fall into quirks mode, which can enable unexpected rendering behaviors and widen the attack surface for XSS.
Use Recommended HTTP Response Headers
Server-side HTTP response headers provide an additional layer of defense that operates independently of application-level encoding:
- X-XSS-Protection: 1; mode=block — Activates the browser's built-in XSS filter and instructs it to block the page rather than sanitize it.
- X-Frame-Options: deny — Prevents the page from being loaded inside a frame, mitigating clickjacking and some mXSS attack paths.
- X-Content-Type-Options: nosniff — Prevents the browser from MIME-type sniffing, which can be exploited to misinterpret response content.
- Content-Security-Policy — One of the most powerful XSS defenses available, allowing developers to define policies that restrict where resources may be loaded from.
- Set-Cookie: key=value; HttpOnly — Prevents JavaScript from accessing session cookies, significantly limiting the impact of a successful XSS attack.
- Content-Type: type/subtype; charset=utf-8 — Ensures the browser interprets the response with the correct content type and character encoding.
Prevent CRLF Injection and Disable Unnecessary HTTP Methods
All user-supplied data must be sanitized before inclusion in HTTP response headers. A CRLF injection attack can allow an attacker to inject arbitrary headers — effectively dismantling CSP, X-XSS-Protection, and other defenses in a single stroke.
The HTTP TRACE method, intended for debugging, reflects request headers back in the response. Injections into request headers combined with a TRACE-enabled server can result in XSS. TRACE and all other unnecessary HTTP methods should be disabled.
Implementing Content Security Policy Effectively
Content Security Policy (CSP) is a browser-enforced security mechanism that specifies which resources a page is permitted to load and from where. It is one of the most effective controls available against XSS, particularly stored and reflected variants.
A CSP is delivered via the Content-Security-Policy HTTP response header and is composed of directives, each governing a specific resource type:
- default-src — The fallback policy for all resource types not covered by a more specific directive.
- script-src — Controls which domains may serve JavaScript.
- style-src — Controls allowed sources for CSS stylesheets.
- img-src — Controls allowed image sources.
- frame-src — Controls which domains may be embedded in frames.
- object-src — Controls plugin sources such as Flash. Setting this to none is strongly recommended.
- connect-src — Restricts the origins to which XHR, WebSocket, and EventSource connections may be made.
- font-src — Controls allowed font sources.
Developers should resist the temptation to use unsafe-inline and unsafe-eval source expressions unless absolutely necessary, as they significantly weaken CSP protections. While many modern applications require these directives for third-party integrations, their use should be carefully scoped and documented.
XSS Protection in JavaScript
For JavaScript applications, several mature libraries provide encoding and sanitization utilities:
Encoder.js offers methods including htmlEncode(), XSSEncode(), numEncode(), and correctEncoding(), covering the most common escaping needs.
DOMPurify is a DOM-only XSS sanitizer for HTML, MathML, and SVG. It prevents DOM clobbering, supports whitelisting, and integrates with popular JavaScript frameworks. It is one of the most widely recommended client-side sanitization libraries.
js-xss provides escaping with whitelist support for Node.js and browser environments, and the xss npm package offers sanitization suitable for server-side rendering pipelines. In jQuery, the .text() method should be preferred over .html() when inserting untrusted data. In YUI, the html() method handles escaping including backtick characters.
XSS Protection in PHP
PHP provides several built-in functions for output encoding. The htmlspecialchars() function encodes the core HTML special characters and should always be invoked with the ENT_QUOTES flag and UTF-8 charset to ensure single quotes are also escaped. Note that htmlspecialchars() does not protect against XSS in JavaScript, style, or URL contexts — additional escaping is required there. The urlencode() function handles URL encoding, and utf8_encode() converts data to UTF-8 for safe processing.
For richer sanitization needs, HTML Purifier is the recommended PHP library. It operates on a whitelist basis, strips invalid HTML constructs, and is straightforward to configure. PHPIDS (PHP-Intrusion Detection System) complements sanitization by detecting when attack patterns are present, allowing the application to respond appropriately without altering the input itself.
The Smarty templating engine provides context-aware escaping via its escape modifier, supporting HTML, URL, JavaScript, CSS, hex, and other encoding modes out of the box.
XSS Protection in Java
Java developers should turn to the OWASP Java Encoder project, which provides encoding utilities for HTML body content, HTML attributes, JavaScript blocks and variables, URL parameters, REST URL segments, and full untrusted URLs. The Coverity Security Library (CSL) complements this with EL-notation support and methods for HTML escape, JavaScript string escape, URL escape, CSS string escape, and color value validation. OWASP ESAPI (Enterprise Security API) provides a comprehensive, context-aware encoding interface covering HTML, HTML attributes, JavaScript, CSS, and URLs.
XSS Protection in .NET
The HttpUtility class (System.Web.HttpUtility) in .NET provides HtmlEncode(), HtmlAttributeEncode(), UrlEncode(), and JavaScriptStringEncode() methods suitable for most standard web applications. For applications dealing with XML output or requiring whitelist-based sanitization, the AntiXssEncoder class (System.Web.Security.AntiXss.AntiXssEncoder), built into .NET 4.5, provides a broader set of encoding methods including XmlEncode(), XmlAttributeEncode(), and UrlPathEncode().
XSS Protection in Python Django
Django's template engine applies auto-escaping by default using the {{ string }} syntax. The escape() function explicitly escapes HTML special characters, while conditional_escape() performs the same operation without double-encoding already-escaped strings. URL encoding is handled by urlencode().
XSS Protection in Ruby on Rails
Rails provides a comprehensive set of sanitization helpers. The sanitize() method encodes user data against a configurable whitelist and strips tags with dangerous protocols such as javascript:. The sanitize_css() method handles CSS context specifically. The h() and html_escape() helpers encode the core HTML special characters, while html_escape_once() avoids double-encoding. The json_escape() method handles JSON output encoding, though it should only be used with valid JSON values.
Open Source Firewalls and Detection Tools
For an additional perimeter-level defense, ModSecurity and IronBee are mature open source web application firewalls that can detect and block XSS payloads before they reach application code.
For testing and detection, developers can use tools such as the OWASP Xenotix XSS Exploit Framework, IronWASP, Acunetix Free, Arachni, and the ImmuniWeb Self-Fuzzer browser extension.
Defending against XSS demands a consistent, context-aware, and layered approach. No single technique — whether input validation, output encoding, CSP, or security headers — is sufficient on its own. The combination of rigorous input validation at ingestion, context-sensitive output escaping at rendering, a well-tuned Content Security Policy, appropriate HTTP response headers, and the use of established security libraries provides the depth of defense necessary to build genuinely secure web applications. Developers who internalize these principles and apply them consistently will eliminate the vast majority of XSS risk from their codebases.
Written by Khalil Shreateh Cybersecurity Researcher & Social Media Expert Official Website: khalil-shreateh.com