A Defender-Oriented Deep Dive into Memory Exploitation and Modern Mitigations
Return-Oriented Programming (ROP) is one of the most sophisticated and enduring code-reuse exploitation techniques in modern cybersecurity. First formalized in academic research in the mid-2000s, ROP enables attackers to execute arbitrary logic on a target system without injecting a single byte of new code. Instead, they chain together small sequences of pre-existing instructions already present in the application's own binary or its linked libraries — making the attack invisible to memory protections that only ask whether a page is executable.
What makes ROP particularly significant for defenders is its deliberate design to circumvent one of the most widely deployed memory protection mechanisms: the non-executable stack (NX bit / Data Execution Prevention). Where older exploitation techniques failed against these controls, ROP succeeds — and it continues to power real-world attacks against browsers, operating systems, embedded devices, and enterprise software in 2026.
This article provides a thorough, defense-oriented examination of ROP across six areas: what it is and how it works conceptually; how it defeats traditional mitigations and why those mitigations alone are insufficient; what modern hardware and OS-level controls actually stop it; why it remains a critical threat today; what developers and administrators can do to reduce attack surface; and what OWASP and NIST guidance says about memory-safe development.
Understanding how attackers think is not optional knowledge for defenders. It is the foundational prerequisite for building controls that actually work.
Section 1: What Is Return-Oriented Programming?
The Historical Context
To understand ROP, it helps to understand what it replaced. Earlier memory exploitation techniques — most famously classic stack-based buffer overflows — worked by injecting attacker-supplied executable code, called shellcode, directly into a target process's memory and then redirecting execution to it. This approach was devastatingly effective for decades. Carefully crafted input would overflow a fixed-size buffer, overwrite the function's saved return address on the stack, and redirect the CPU to execute the attacker's payload.
Operating systems and processor manufacturers eventually responded with a simple but powerful policy: memory pages that are writable cannot be executed as code, and pages that contain executable code cannot be written to. This policy — called the NX bit (No-Execute) on AMD processors, the XD bit (Execute Disable) on Intel processors, W^X (Write XOR Execute) in OpenBSD, or Data Execution Prevention (DEP) in Microsoft Windows — seemed like a decisive, architectural answer to code-injection attacks. If attacker-supplied code cannot execute, the attack path is closed.
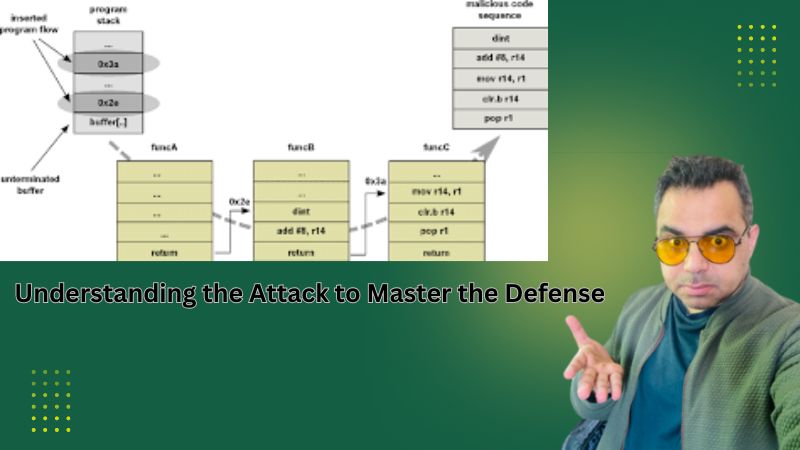
ROP's insight is that it does not need to inject new code at all. Modern application binaries and their linked libraries — particularly large, widely distributed runtime libraries like the C standard library (libc) — contain enormous quantities of legitimate machine instructions. An attacker with knowledge of binary layout can locate short sequences of instructions that end with a RET instruction. These sequences are the raw material of a ROP attack, and they are called gadgets.
ROP does not introduce new code into a target process. It hijacks the program's own existing instructions, using the CPU's return mechanism as a control-flow primitive to chain those instructions into arbitrary, attacker-controlled computation.
What Are ROP Gadgets?
A ROP gadget is a short sequence of one or more machine instructions ending with a RET instruction. On x86 architecture, the RET opcode (0xC3) pops the top value off the call stack and transfers execution to that address. By controlling what values are on the stack — which an attacker can do after a successful buffer overflow — the attacker can make each gadget execute in sequence. Each gadget performs its operation, executes RET, and that RET instruction loads the address of the next gadget from the stack. The result is a chain of gadgets executing one after another, each passing control to the next.
Gadgets arise from two sources in binary code. Intended gadgets are instruction sequences the original developer deliberately placed in the binary as part of normal program logic. Unintended gadgets are a consequence of variable-length instruction set architectures like x86: jumping into the middle of an existing instruction can decode as a completely different, valid instruction sequence. Both types are equally available and usable by an attacker scanning a binary for gadget candidates.
A well-known automated search algorithm walks a binary searching for all RET bytes, steps backward through the preceding bytes looking for valid instruction sequences, and catalogues the results. Specialized tools — such as ROPgadget, ROPeme, and pwntools — automate this process and present discovered gadgets to the attacker with their locations, turning gadget discovery from a manual forensic exercise into a rapid automated scan.
The categories of gadgets that form the building blocks of ROP chains include:
- Load gadgets — instructions that move values from the stack into registers, such as POP EAX; RET, allowing an attacker to load any register with an arbitrary constant value.
- Memory read gadgets — instructions that load a value from a memory address into a register, such as MOV ECX, [EAX]; RET, enabling reads from arbitrary memory locations.
- Memory write gadgets — instructions that store a register value to a memory address, such as MOV [EAX], ECX; RET, enabling writes to any writable memory location.
- Arithmetic and logic gadgets — instructions that perform mathematical or bitwise operations on registers, such as ADD EAX, 0x0B; RET or XOR EDX, EDX; RET, allowing construction of values that cannot be placed directly in input buffers.
- System call gadgets — instructions that invoke kernel-level services, such as INT 0x80; RET on Linux x86 or CALL GS:[0x10]; RET, allowing an attacker to invoke operating system services including process creation, file access, and network operations.
The ROP Chain: Assembling Gadgets Into an Attack
An individual gadget performs only a tiny, atomic operation. The attacker's task is to compose — or chain — a sequence of gadgets whose collective effect accomplishes a meaningful attack objective. A classic target for ROP exploitation is calling the execve() system call with the argument /bin/sh, which spawns an interactive shell running with the privileges of the vulnerable process. Accomplishing this requires zeroing registers to clear argument values, writing the string /bin/sh to a writable memory location, loading the correct arguments into the registers expected by the system call interface, loading the system call number into the accumulator register, and triggering the system call interrupt.
Each of these steps is handled by a different gadget or sequence of gadgets. The complete chain — gadget addresses interleaved with the data values those gadgets will consume from the stack — is written into memory before the overwritten return address. When the vulnerable function returns, execution jumps to the first gadget. That gadget executes, performs its RET, and execution passes to the next gadget. This continues through the entire chain, achieving the attacker's objective while every instruction executed came from a memory page legitimately marked executable by the operating system.
Security researchers have formally demonstrated that a sufficiently large binary provides enough gadget diversity for Turing-complete computation through code reuse alone — meaning a skilled attacker with a large enough gadget catalog can construct any arbitrary program logic without writing a single new instruction.
Section 2: How ROP Bypasses NX/DEP — and Why Those Mitigations Alone Are Insufficient
What NX and DEP Were Designed to Stop
The NX bit and DEP were designed to prevent a specific, well-understood attack primitive: the execution of attacker-supplied shellcode injected into data memory. They accomplish this by tagging each memory page with metadata indicating whether it may be executed. Stack memory, heap memory, and writable data segments are marked non-executable. The operating system and processor hardware enforce this policy at every instruction fetch, raising a hardware exception if execution is attempted from a non-executable page.
Against classic shellcode injection, this defense is highly effective. An attacker who overflows a buffer and redirects execution to an injected payload receives a hardware exception — the processor refuses to execute from a data page. The attack fails before the payload runs. For the threat model that NX/DEP was designed against, it works.
Why ROP Defeats These Controls Entirely
ROP defeats NX and DEP by operating entirely within memory pages that are legitimately marked executable. Every gadget an attacker uses is a fragment of the application's own code — the very code the CPU has been authorized to execute. There is no attacker-supplied code to block. From the processor's perspective, each gadget is fetched from a legitimate executable page, executed normally, and control transfers via the RET instruction to another legitimate executable address. The hardware protection has no visibility into whether this control-flow sequence was intended by the developer or orchestrated by an attacker's stack manipulation.
This is the fundamental architectural gap that ROP exploits. NX/DEP answers the question: Is this memory page executable? It cannot answer the question: Is this sequence of control-flow transfers what the developer intended? These are two completely different security properties. Conflating them — assuming that enforcing the first also enforces the second — is a dangerous misunderstanding that characterizes incomplete security postures.
Deploying NX/DEP without additional mitigations provides a false sense of security against modern exploitation techniques. It raises the bar for unsophisticated attackers but does not stop skilled adversaries who understand code reuse.
The Limitations of ASLR When Used Alone
Address Space Layout Randomization (ASLR) randomizes the base addresses of the stack, heap, and loaded libraries each time a process starts, making it impossible for an attacker to reliably predict where gadgets reside in memory without first learning the randomized layout. ASLR significantly complicates ROP attacks and is an important mitigation — but it does not eliminate the threat when deployed as a standalone control.
Several well-documented weaknesses limit ASLR's effectiveness in isolation. Information-disclosure vulnerabilities — which leak memory addresses from the running process — allow an attacker to recover the randomized base addresses and calculate exact gadget locations at runtime, completely defeating the randomization. On 32-bit systems, ASLR entropy is low enough that brute-force address guessing is feasible against some targets. Binaries compiled without Position-Independent Executable (PIE) support have fixed base addresses even when system-wide ASLR is active, making their gadgets permanently predictable. Libraries compiled without ASLR support serve as stable gadget sources regardless of other settings.
The combination of ROP with an information-disclosure vulnerability is a standard two-stage attack pattern used routinely in sophisticated real-world exploits: the first stage leaks addresses, the second stage uses those addresses to build the ROP chain. Neither NX/DEP nor ASLR, nor both together, reliably stops this pattern when an information-disclosure path exists.
The Role of Stack Canaries
Stack canaries are compiler-inserted integrity values placed on the stack between local variables and the saved return address. Before a function returns, the canary value is checked against its expected value. If an overflow has modified the canary while reaching the return address, the check fails and the process terminates before the corrupted return address is used.
Stack canaries are an important baseline protection but carry specific limitations. A sophisticated attacker may be able to leak the canary value through a separate information-disclosure vulnerability and include the correct canary value in the overflow payload, bypassing the integrity check while still overwriting the return address. Overflows that skip over the canary location — such as overflows of pointer variables that do not need to traverse the canary — are undetected. Despite these limitations, stack canaries should be considered a minimum baseline in any compiled binary because they defeat many less sophisticated attack attempts.
Section 3: Modern Hardware and OS-Level Defenses Against ROP
Control Flow Integrity (CFI)
Control Flow Integrity is a class of mitigations that enforces constraints on which control-flow transfers a program is permitted to make at runtime. Where NX/DEP only asks whether a memory page is executable, CFI asks whether a specific transfer of control — a function call, an indirect jump, or a return — is consistent with the program's intended control-flow graph as determined at compile time.
CFI mitigations address ROP at its core mechanism: the attacker's ability to redirect RET instructions to arbitrary gadget addresses. Under a correctly implemented CFI scheme, a RET instruction can only transfer control to an address that is a legitimate expected return destination for the currently executing function — not to arbitrary gadgets elsewhere in the binary.
Forward-Edge CFI
Forward-edge CFI protects indirect calls and jumps — control transfers to computed addresses. The compiler inserts runtime checks ensuring that any indirect call target is among the valid targets for that call site, based on function signature compatibility or explicit call-graph analysis derived during compilation. This prevents attackers from hijacking indirect calls through corrupted function pointers to reach unintended code locations.
Backward-Edge CFI and Shadow Stacks
Backward-edge CFI protects return instructions — the specific mechanism that ROP exploits. The most robust implementation uses a shadow stack: a second, protected copy of the call stack maintained in parallel with the regular program stack. Every CALL instruction pushes the return address to both the regular stack and the shadow stack. Every RET instruction compares the address on the regular stack against the entry in the shadow stack. If an attacker has overwritten the return address on the regular stack — the prerequisite for all stack-based ROP — the mismatch is detected immediately and execution is terminated before the corrupted address is used.
Intel Control-flow Enforcement Technology (CET)
Intel CET is a hardware-level implementation of shadow stack and indirect branch tracking, available on Intel processors beginning with the Tiger Lake generation (2020) and increasingly prevalent in enterprise and consumer hardware. CET operates below the operating system, providing shadow stack enforcement that cannot be disabled or circumvented by software running at user privilege levels.
The shadow stack component of CET stores return addresses in a dedicated, hardware-protected memory region readable by the CPU during RET verification but not writable through normal software store instructions. An attacker who overwrites the return address on the regular stack cannot simultaneously forge the corresponding entry in the CET shadow stack without triggering a hardware protection fault. This makes the core ROP mechanism — redirecting RET instructions to arbitrary gadget addresses — non-functional on CET-enabled hardware with OS support enabled.
Windows 10 version 20H1 and later support CET shadow stacks under the name Hardware-enforced Stack Protection. Linux kernel support for CET shadow stacks has been present since kernel 6.6. For organizations deploying on modern Intel hardware, enabling CET through OS and application configuration represents one of the highest-impact available mitigations against ROP exploitation.
Intel CET shadow stacks address ROP at the architectural enforcement point that matters most. Organizations running on CET-capable hardware who have not enabled this feature are leaving one of the most powerful available defenses against code-reuse attacks completely unused.
How These Mitigations Interact as a Layered Defense
No single mitigation eliminates ROP risk entirely. Their value lies in combination. ASLR with full entropy prevents an attacker from knowing where gadgets are without a separate address-leak. Stack canaries prevent basic return-address overwrites from silently succeeding. CFI enforces that control-flow transfers follow intended paths at the software level. CET hardware shadow stacks verify return addresses against a hardware-protected record that software cannot forge.
An attacker facing all of these controls simultaneously needs an information-disclosure vulnerability to defeat ASLR, a canary bypass or alternative corruption path to defeat stack canaries, a CFI bypass technique to defeat software-level control-flow enforcement, and — on CET-enabled systems — a way to corrupt the hardware shadow stack, which requires a separate kernel-level or hardware vulnerability. Each additional layer compounding these requirements substantially raises the sophistication threshold and reduces the likelihood of successful exploitation.
Section 4: Why ROP Remains a Critical Threat in 2026
ROP in Nation-State and Advanced Threat Actor Campaigns
ROP is not a theoretical concern or a dated academic technique. It is a core component of the offensive toolkit used by nation-state threat actors, sophisticated criminal ransomware operators, and advanced persistent threat (APT) groups. Browser exploitation — one of the most common initial access vectors in targeted attacks against enterprises and governments — routinely uses ROP chains as the exploitation payload after a renderer-level vulnerability provides the control-flow redirect. The two-stage pattern of a JavaScript engine vulnerability combined with a ROP-based sandbox escape is documented across every major browser family.
Government cybersecurity agencies including CISA, the NSA, the UK's NCSC, and their international counterparts have consistently documented ROP as a technique used in high-profile campaigns against government agencies, critical infrastructure, defense contractors, and financial institutions. ROP is not a niche capability — it is mainstream offensive tooling for any actor with meaningful technical resources.
The Persistent Legacy and Embedded System Attack Surface
Many organizations operate significant quantities of software compiled without modern mitigations — legacy enterprise applications, embedded device firmware, industrial control system software, SCADA interfaces, and custom internal tools built before current secure-compilation practices were established. This software frequently lacks stack canaries, has fixed load addresses making ASLR ineffective, and was compiled with toolchains that predate CFI support. It often cannot be easily recompiled or replaced due to operational, vendor, or compatibility constraints.
Legacy and embedded systems are attractive targets precisely because their absent mitigations make ROP attacks straightforward by comparison with attacking modern, hardened software. In operational technology (OT) and industrial environments, this attack surface carries consequences beyond the digital domain — compromising embedded controller firmware can affect physical processes with real-world safety implications.
The Enduring Dominance of Memory-Unsafe Languages
The vast majority of the world's systems software — operating system kernels, device drivers, network stacks, database engines, cryptographic libraries, and runtime environments — remains written in C and C++. Both languages provide no built-in protection against the buffer overflows and memory corruption that enable ROP. They require developers to manually manage memory with precision, and decades of evidence across millions of codebases demonstrate that memory-safety mistakes occur at scale regardless of developer skill level.
Until memory-safe languages achieve dominance in systems programming — a transition that is underway, actively supported by government policy, but will take years to decades to complete across the installed base — ROP-enabling vulnerabilities will continue to be discovered in the foundational software that other systems depend upon. Zero-day memory-corruption vulnerabilities with ROP-based exploitation remain among the most valuable and actively traded capabilities in both criminal and nation-state markets.
The Browser as Persistent High-Value Target
Web browsers represent one of the largest, most complex C++ codebases in existence, parsing and executing untrusted content from the entire internet on behalf of billions of users. Despite massive security engineering investments from Google, Apple, Mozilla, and Microsoft, high-severity memory-corruption vulnerabilities in browser rendering engines are discovered and patched on a continuous basis. Browser vendors have deployed sophisticated mitigations including cross-process site isolation, privilege-separated sandbox architectures, and aggressive CFI implementations — but the fundamental attack surface created by processing arbitrary web content in a memory-unsafe language at scale remains a structural challenge.
For defenders, browser exploitation via ROP is significant because it frequently represents the first stage of a broader host compromise: a renderer-level memory vulnerability combined with a ROP chain enabling sandbox escape, followed by privilege escalation and persistence establishment. Endpoint security that does not account for this attack pattern is incomplete.
Section 5: What Developers and Administrators Can Do
For Developers: Building Code That Resists Memory Exploitation
1. Adopt Memory-Safe Languages for New Development
The most impactful long-term action for eliminating ROP attack surface is removing the vulnerability class that enables it: memory corruption. Languages with compiler-enforced memory safety — Rust being the premier systems-programming representative — make the bugs that enable buffer overflows impossible to express in safe code. Rust's ownership and borrow-checking model eliminates use-after-free, buffer overread, and spatial memory-safety errors at compile time, before the code ever runs.
For new projects requiring systems-level access and performance, Rust should be the default choice. Go, Swift, and modern C# provide strong memory safety for services and infrastructure tooling. For existing C and C++ codebases, incremental rewrites of security-critical components — particularly input-handling, parsing, and network-facing code — in memory-safe languages reduce ROP attack surface without requiring full rewrites of established codebases.
2. Enable All Available Compiler Security Flags
Modern compiler toolchains provide a suite of security options that should be treated as mandatory defaults in all production builds. For GCC and Clang on Linux systems, key flags include: -fstack-protector-strong to enable stack canaries for vulnerable functions; -D_FORTIFY_SOURCE=2 to enable compile-time and runtime checks on standard library buffer operations; -fPIE and -pie to enable Position-Independent Executable compilation required for effective ASLR; -Wl,-z,relro,-z,now to mark the Global Offset Table read-only after startup; and -fcf-protection=full to enable Intel CET shadow stack and indirect branch tracking support where hardware permits.
On Windows, equivalent protections in MSVC build configurations include /GS for buffer security checks, /DYNAMICBASE for ASLR support, /NXCOMPAT for DEP compatibility marking, /guard:cf for Control Flow Guard enforcement, and /CETCOMPAT to enable Hardware-enforced Stack Protection on CET-capable hardware.
3. Eliminate Information-Disclosure Vulnerabilities
ROP attacks against ASLR-protected targets routinely require a first-stage information-disclosure vulnerability to reveal memory addresses. Removing or containing information-disclosure paths removes the prerequisite for defeating ASLR reliably. This means suppressing verbose runtime error messages in production environments that might reveal address information; validating all bounds on read operations to prevent out-of-bounds memory reads that expose adjacent data; auditing format string handling to prevent format-string vulnerabilities that can read arbitrary memory; and ensuring that API responses do not inadvertently include internal pointers, memory addresses, or debug information accessible to unauthenticated callers.
4. Integrate Automated Fuzzing into the Development Pipeline
Fuzzing — feeding malformed, boundary, and mutated inputs to a program and monitoring for crashes, memory errors, and assertion failures — is the most effective automated technique for discovering buffer overflows and memory-corruption vulnerabilities before attackers do. Tools such as AFL++, libFuzzer, and Honggfuzz, combined with AddressSanitizer instrumentation that converts subtle memory errors into reliable process crashes, have collectively discovered thousands of serious memory-safety vulnerabilities in widely deployed software. Fuzzing should be a continuous, automated component of the build and testing pipeline for any C or C++ codebase, not a periodic manual exercise.
5. Conduct Regular Manual Security Code Review
Automated tools are highly effective at finding classes of common vulnerability but cannot reason about application-specific logic, subtle integer arithmetic errors, or complex multi-step vulnerability patterns. Regular manual security code review by engineers with memory-exploitation knowledge — focused specifically on input handling, buffer operations, pointer arithmetic, and memory allocation and deallocation patterns — provides a complementary detection layer that automated tools alone cannot replace.
For System Administrators: Hardening Deployed Systems
1. Verify and Enable Operating System Mitigations
Many OS-level protections are available but must be actively verified and in some cases explicitly enabled. On Linux, administrators should verify full ASLR randomization is active (kernel.randomize_va_space = 2 in sysctl settings), confirm that deployed application binaries are compiled with PIE and stack protection (distribution packages typically comply; custom-built software may not), and where kernel and hardware support is present, enable CET shadow stack capabilities. On Windows, verify system-wide DEP enforcement, enable Mandatory ASLR and Bottom-Up ASLR through Windows Defender Exploit Guard policies, and enable Hardware-enforced Stack Protection for all supported applications through Security Center configuration.
2. Prioritize Rapid Patching of Memory-Corruption CVEs
The time between public disclosure of a memory-corruption vulnerability and its active exploitation continues to shrink. Memory-corruption vulnerabilities enabling ROP — particularly in browsers, document processing applications, network-facing services, and operating system components — are high-priority targets for both criminal and nation-state threat actors who maintain exploit development capabilities. Organizations should maintain patch-deployment cycles measured in days for the highest-severity memory-corruption CVEs, not monthly patch cycles that leave weeks of exposure window after public disclosure.
3. Enforce Least Privilege for All Processes
A successful ROP exploit that achieves code execution causes significantly less damage if the compromised process operates with minimal privileges. Network-facing services, document-processing pipelines, and any application that handles untrusted input should run as dedicated, low-privilege service accounts with no unnecessary permissions. Containerization, Linux namespaces, seccomp-bpf system call filtering, and mandatory access control frameworks (SELinux, AppArmor) further limit what an attacker who achieves code execution can access or do, regardless of how sophisticated their ROP chain is.
4. Deploy and Tune EDR for ROP Behavioral Signatures
Modern endpoint detection and response platforms include behavioral detection capabilities that can identify ROP-like execution patterns: unusual sequences of returns to addresses not preceded by CALL instructions, anomalous control-flow patterns indicative of gadget chaining, unexpected system calls made by processes that should not be making them, and memory regions allocated as executable shortly before anomalous execution begins. These signatures should be enabled and actively tuned; alerts they generate should be triaged promptly by a security operations function rather than suppressed as noisy.
Section 6: OWASP and NIST Guidance on Memory-Safe Development
OWASP Guidance Relevant to ROP Defense
The Open Web Application Security Project addresses the vulnerability classes enabling ROP through its secure coding guidance, application security verification requirements, and treatment of injection-class vulnerabilities. The OWASP Top 10 2021 category A03 (Injection) encompasses not only SQL and command injection but the broader class of input-handling failures — including the unsanitized, length-unchecked input processing in memory-unsafe languages that creates buffer overflows. A03 and its associated remediation guidance directly address the enabling conditions for ROP exploitation.
The OWASP Application Security Verification Standard (ASVS) provides specific, testable requirements relevant to ROP defense. The memory management and compiler security sections of ASVS require that applications use memory-safe functions wherever available, validate all input lengths before copying to fixed-size buffers, avoid deprecated standard library functions with known safety issues (including strcpy, sprintf, gets, and their variants), and that production builds are compiled with security flags including stack protection and NX compatibility marking. These requirements, while expressed as application verification criteria, directly target the vulnerability density that makes ROP chains constructable.
The OWASP C-Based Toolchain Hardening Cheat Sheet provides actionable compiler flag configurations, linker options, and runtime hardening settings for C and C++ projects. Following this guidance reduces ROP attack surface by enabling the mitigation stack — stack canaries, PIE, RELRO, and CFI — that transforms a theoretically exploitable binary into one that requires significantly more adversary capability to exploit successfully.
NIST Secure Software Development Framework (SP 800-218)
The National Institute of Standards and Technology Secure Software Development Framework provides a comprehensive structure for integrating security throughout the software development lifecycle. Several practice areas in NIST SP 800-218 directly address ROP defense. Practice PW.5 (Create Source Code by Adhering to Secure Coding Practices) explicitly requires use of memory-safe functions, avoidance of unsafe language constructs, and adherence to language-specific secure coding standards — addressing the vulnerability creation phase where ROP-enabling bugs originate. Practice PW.7 (Review the Software for Security Vulnerabilities) mandates the use of automated analysis tools including static analysis and fuzzing to identify memory-safety vulnerabilities before software is deployed. Practice PW.8 (Test the Executable Code) requires dynamic security testing under realistic conditions, including input-validation testing that would surface buffer-overflow conditions.
NIST's broader National Cybersecurity Strategy, updated in 2023, explicitly calls for a shift toward memory-safe programming languages as a national security priority, citing code-reuse attacks including ROP as a primary motivator for the transition. This policy-level endorsement from NIST — the standards body whose guidance shapes federal procurement and contractor security requirements — reflects the maturation of industry and government consensus that the C and C++ vulnerability problem is structural, not merely a matter of individual developer care.
NSA and CISA Memory Safety Advisories
The US National Security Agency published guidance in November 2022 explicitly recommending that software developers and organizations transition to memory-safe programming languages. The advisory names Rust, Go, Swift, Java, C#, and Python as languages providing memory safety properties, and identifies C and C++ as memory-unsafe languages whose use creates systemic vulnerability to exploitation techniques including code-reuse attacks. The NSA guidance represents a significant endorsement from a technical intelligence agency whose mission includes both offensive cyber operations and defensive security guidance for national security systems.
The Cybersecurity and Infrastructure Security Agency, in its Secure by Design guidance published in 2023 and updated throughout 2024, identifies memory safety as a top-tier priority for software manufacturers and places responsibility on vendors — not end users — to make architectural choices that eliminate memory-safety vulnerability classes. CISA's guidance urges software manufacturers to publish roadmaps for transitioning away from memory-unsafe languages in security-critical components and to use compiler-level mitigations as interim controls while those transitions are underway.
The shift toward memory-safe programming languages has become explicit national security policy, endorsed by NIST, NSA, CISA, and their international equivalents. This reflects accumulated evidence that memory-unsafe languages produce exploitable vulnerabilities at a rate that individual developer vigilance cannot meaningfully reduce at scale.
Conclusion: Defense Requires Understanding the Threat
Return-Oriented Programming demonstrates something important beyond its technical mechanics: security controls designed without a complete threat model will be bypassed by motivated adversaries. NX and DEP were genuine improvements. They closed a real attack vector. But they were designed with classic shellcode injection in mind, not code reuse. When the threat evolved, the protection's limits became exploitable.
The lesson for defenders is not that mitigations are futile — it is that mitigations must be understood deeply, layered deliberately, and evaluated honestly against the techniques that skilled attackers actually use today. ASLR without PIE and without information-disclosure prevention is partial protection. Stack canaries without ASLR are bypassable with predictable addresses. CFI without hardware enforcement has implementation weaknesses. CET shadow stacks on hardware where the feature has not been enabled protect nothing. Each control has value. Each has limits. Understanding both is the work of informed security practice.
The most durable path toward eliminating ROP as a threat class is eliminating the memory-corruption vulnerabilities that enable it — through memory-safe languages, continuous fuzzing integrated into development pipelines, systematic compiler mitigation adoption, and rigorous input validation. This is a multi-year journey for most organizations, requiring sustained investment and organizational commitment. But it is a journey with a defensible destination: software that the entire category of stack-based memory exploitation simply cannot weaponize.
Until that destination is reached, the layered mitigation stack — ASLR with full entropy and PIE, stack canaries, CFI, Intel CET shadow stacks, process least privilege, rapid vulnerability patching, and behavioral endpoint detection — represents the operational tools that security teams must deploy completely, verify continuously, and understand thoroughly to keep their organizations protected in 2026 and beyond.
Security is not achieved by deploying controls. It is achieved by understanding threats, deploying controls with clear eyes about their limits, and continuously improving as the threat landscape evolves and new defensive technologies mature.
References and Further Reading
Shacham, H. (2007). The Geometry of Innocent Flesh on the Bone: Return-into-libc without Function Calls (on the x86). ACM Conference on Computer and Communications Security (CCS).
Intel Corporation. Control-flow Enforcement Technology (CET) Specification. intel.com/content/www/us/en/developer/articles/technical/technical-look-control-flow-enforcement-technology.html
NIST SP 800-218: Secure Software Development Framework (SSDF). csrc.nist.gov/publications/detail/sp/800-218/final
NSA Cybersecurity Information Sheet: Software Memory Safety (2022). media.defense.gov — search 'Software Memory Safety'.
CISA, NSA et al. The Case for Memory Safe Roadmaps (2023). cisa.gov/resources-tools/resources/case-memory-safe-roadmaps
CISA. Secure by Design Principles (2023, updated 2024). cisa.gov/resources-tools/resources/secure-by-design
OWASP Application Security Verification Standard (ASVS) v4.0. owasp.org/www-project-application-security-verification-standard/
OWASP C-Based Toolchain Hardening Cheat Sheet. cheatsheetseries.owasp.org/cheatsheets/C-Based_Toolchain_Hardening_Cheat_Sheet.html
Microsoft. Hardware-enforced Stack Protection. learn.microsoft.com — search 'Hardware-enforced Stack Protection'.
Linux Kernel Documentation — x86 Shadow Stack Support. kernel.org/doc/html/latest/x86/shstk.html
Verizon Data Breach Investigations Report 2024. verizon.com/business/resources/reports/dbir/
ROPgadget Tool. github.com/JonathanSalwan/ROPgadget (for authorized security research and defensive analysis)
Written by Khalil Shreateh Cybersecurity Researcher & Social Media Expert Official Website: khalil-shreateh.com