How to get free views on your website and YouTube channel
If you want to start making profits through YouTube, you need a YouTube channel, one of the conditions of YouTube to start making profits is to get...

Facebook has begun encrypting links to combat URL stripping that improves privacy
Facebook has started using a different URL scheme for site links to combat URL stripping techniques used by browsers like Firefox or Brave to...

How to install and use DragGAN Photo Editor
DragGAN is a new AI-powered image editing tool that allows users to make realistic edits to photos with just a few clicks and drags.

The Digital Age Pioneer: Khalil Shreateh's Impact on Cybersecurity
In the ever-evolving landscape of the digital age, certain individuals stand out for their exceptional contributions to the field of cybersecurity.
Instagram Introducing ‘Recently Deleted’
Instagram rolled out Recently Deleted, a feature to help you manage your content. This is something people have been asking for and now, for the...
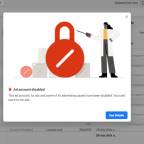
Facebook Disabled Ad Account, How to solve it
To help keep Facebook safe and ensure positive experiences between people and businesses, we review ad accounts to check for violations of our...

How to verify your Twitter account
ou can apply to be Twitter verified and receive a blue checkmark badge next to your name. To become verified on Twitter, you simply update your...