In this article iam explaining the security risk behind Private Registration via domain by proxy company, hopefully they patch this vulnerability ASAP.
Article Index:
. Intro
. Spam/Scam Vulnerability
. Security Risk
Intro (Wikipedia):
Domains by Proxy (DBP) is an Internet company owned by GoDaddy founder Bob Parsons. It offers domain privacy services through partner domain registrars such as Go Daddy and Wild West Domains.
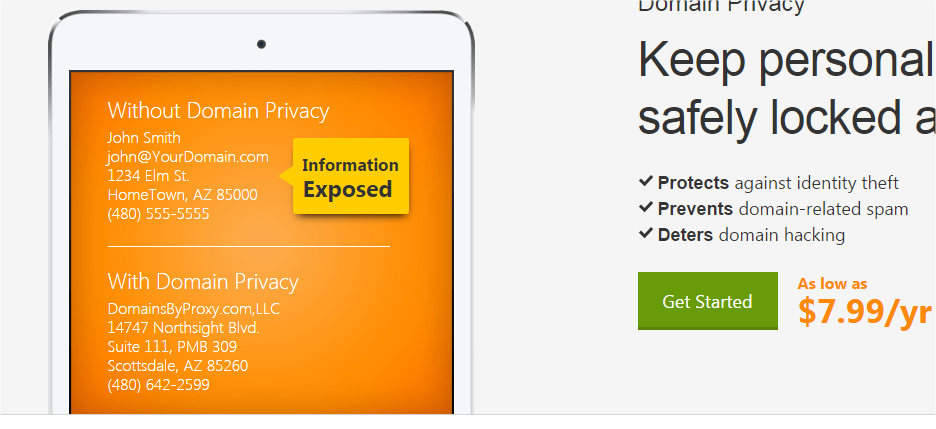
Subscribers list Domains by Proxy as their administrative and technical contacts in the Internet's WHOIS database, thereby delegating responsibility for managing unsolicited contacts from third parties and keeping the domains owners' personal information secret.
Over 9,850,000 domain names currently use the Domains by Proxy service.
Checking information about ownership of a domain name
WHOIS is a query and response protocol that is widely used for querying databases that store the registered users or assignees of an Internet resource, such as a domain name, an IP address block, or an autonomous system, but is also used for a wider range of other information.
Spam/Scam Vulnerability
Note: For security purposes I will not write how to exploit this vulnerability in wide range, the example will be on my own website khalil-shreateh.com
Domains by Proxy (DBP) offers keeping domains admins personal information secret, and this includes their emails. However many admins buy this service because they don’t want to disclose their emails.
DBP has big clients such as (GoDaddy.com, bluerazor.com and wildwestdomains.com).
More: https://uk.godaddy.com/domainaddon/private-registration.aspx
When buying Private Registration your personal info will be hidden from WHOIS queries, including your email address, but this is not as what you think, Spam/Scammers can still email you, their emails will received directly to your email inbox folder, interesting hmmm.
So how Spammers/Scammers can email me while they don’t know my email address?
When you buy Private Registration your domain will be under domainsbyproxy.com despite that you registered it from Godaddy or any other company.
Spam/Scammers can use an email redirect vulnerability in domainsbyproxy.com to send you an email, and to do that simply they add your website as a user name (
I did a Google search and I was able to harvest thousands of emails registered under Private Registration.
Security Risk
Talking bout security risk here is an open field, We can place questions to make the security risk here gives a different meaning than just sending Spam/Scam emails:
- Why this vulnerability is good for Spammers/Scammers?
- Why i should hide my email address from being disclose to public?
- What if many people got my private email address?
- Do you use your email address to register in online payments websites such as Paypal.com?
- How much your website is secure against vulnerabilities?
After giving answers to the above questions you can know how much the security risk we are talking here about this Private Registration email vulnerability.
Scenario
Using one of public known free CMS on a website, installed several plugins.
One of those plugins is vulnerable to Cross Site Scripting (XSS) attack. And as we know this exploit could be used to steal admin cookies and so the attacker can login to the website admin panel and take a full control over the website.
The attacker or the hacker simply can user the Private Registration vulnerability to forward his XSS attack to the victim.
At the end of this article our conclusion is a question: Why anyone can email me while I paid for a private registration?
I hope this vulnerability could be Patched ASAP as iam forwarding this article to Godaddy company.