-
How to Create AI-Generated 360° Panorama Photos and Post Them on Facebook
- Details
- 20

Boost Your Facebook Reach with AI-Powered 360° Photos — Step-by-Step Guide How to Create AI-Generated 360° Panorama Photos and Post Them on Facebook
Did you know that Facebook gives extra algorithmic reach to 360° photo posts? Unlike regular images, 360° photos are rare, interactive, and highly engaging — users can drag with their mouse or tilt their phone to look around inside the image. Facebook's algorithm actively...
Read more: How to Create AI-Generated 360° Panorama Photos an...
-
How to Extract Cookies from Your Mobile Phone
- Details
- 10

How to Get Session Cookies from Your Smartphone to Download Instagram Videos In previous tutorials on the Khalil Shreateh YouTube channel, we covered how to extract browser cookies on desktop using a Chrome extension. In this tutorial, we take it a step further — extracting cookies directly from your iPhone or Android smartphone using a free open-source app called ProxyPin.
This is especially useful if you want to use...
-
Facebook Account Security
- Details
- 15139

Facebook Account Security
By Khalil Shreateh — Information Security
Are you aware that your account could be at risk?
Many people have had their accounts hacked. If it has happened to you, or you know someone it happened to, you are not alone. From phishing pages that steal your login credentials, to malware files (.exe) distributed through...
-
Securing the Modern Web: An In-Depth Look at the Chrome DevTools Security Panel
- Details
- 46

Securing the Modern Web: An In-Depth Look at the Chrome DevTools Security Panel The digital landscape has shifted from an era of optional encryption to one where secure origins are the non-negotiable foundation of the web platform. This transition is not merely a cosmetic change or a push for a "green lock" icon in the address bar; it is a fundamental response to the increasing sophistication of man-in-the-middle (MiTM)...
Read more: Securing the Modern Web: An In-Depth Look at the C...
-
Return-Oriented Programming: Understanding the Attack to Master the Defense
- Details
- 52
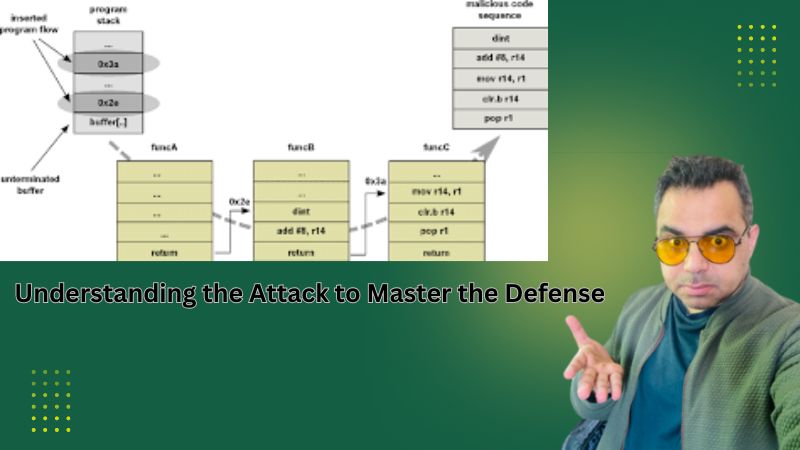
Return-Oriented Programming Explained: How Attackers Reuse Your Code — and How Defenders Fight Back A Defender-Oriented Deep Dive into Memory Exploitation and Modern Mitigations
Return-Oriented Programming (ROP) is one of the most sophisticated and enduring code-reuse exploitation techniques in modern cybersecurity. First formalized in academic research in the mid-2000s, ROP enables attackers to execute arbitrary logic on a target system without...
Read more: Return-Oriented Programming: Understanding the Att...
-
SQL Injection, Defensive Strategies & OWASP Guidelines
- Details
- 59

SQL Injection Demystified: How Attackers Think and How Defenders Win A Comprehensive Cybersecurity Awareness Reference Published May 2026 | Security Awareness Series
Introduction: Why Web Application Security Matters
Web applications are the backbone of modern digital life — from banking portals to e-commerce platforms, healthcare records to government services. Yet they remain among the most frequently targeted...
Read more: SQL Injection, Defensive Strategies & OWASP Guidel...
-
Network Security Bible: A Comprehensive Cybersecurity Awareness and Research Guide
- Details
- 49
Network Security Bible: The Complete Cybersecurity Awareness Guide for Practitioners and Organizations Why Network Security Demands a Unified Discipline
Network security spans an exceptionally broad range of disciplines — from management philosophy and governance policy to the deepest mechanics of operating system kernels, cryptographic algorithms, and wireless radio transmission. For decades, practitioners seeking comprehensive guidance were...
Read more: Network Security Bible: A Comprehensive Cybersecur...
-
Network and System Security: A Comprehensive Cybersecurity Awareness and Research Guide
- Details
- 50

Network and System Security: What Every Organization Must Know to Survive the Modern Threat Landscape The Expanding Attack Surface of Modern Organizations
Organizations today are linking their systems across enterprise-wide networks, virtual private networks, cloud environments, and mobile infrastructure while simultaneously increasing their exposure to customers, competitors, and adversaries on the open Internet. The security market continues to...
Read more: Network and System Security: A Comprehensive Cyber...
-
Understanding Error-Based SQL Injection in ASP/ASPX Applications: A Security Awareness Guide
- Details
- 44
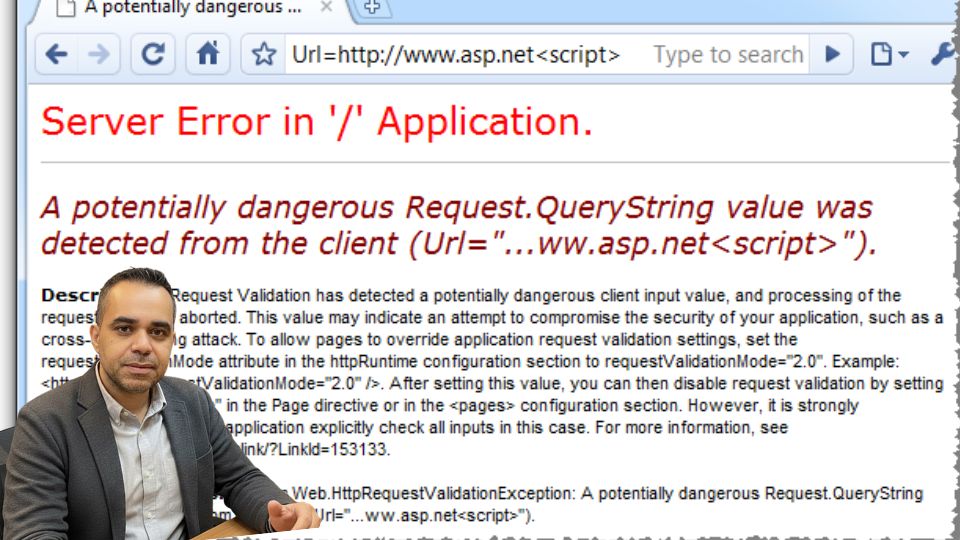
Error-Based SQL Injection in ASP/ASPX Applications: What Attackers Know That Developers Don't Why ASP and ASPX Applications Remain High-Value Targets
Web applications built on Microsoft's ASP and ASP.NET (ASPX) frameworks have powered some of the world's most widely deployed enterprise and public-facing systems for decades. Despite advances in secure development tooling and growing awareness of application security, SQL injection remains one...
Read more: Understanding Error-Based SQL Injection in ASP/ASP...
-
XSS Protection for Developers: A Complete Guide to Securing Web Applications
- Details
- 38
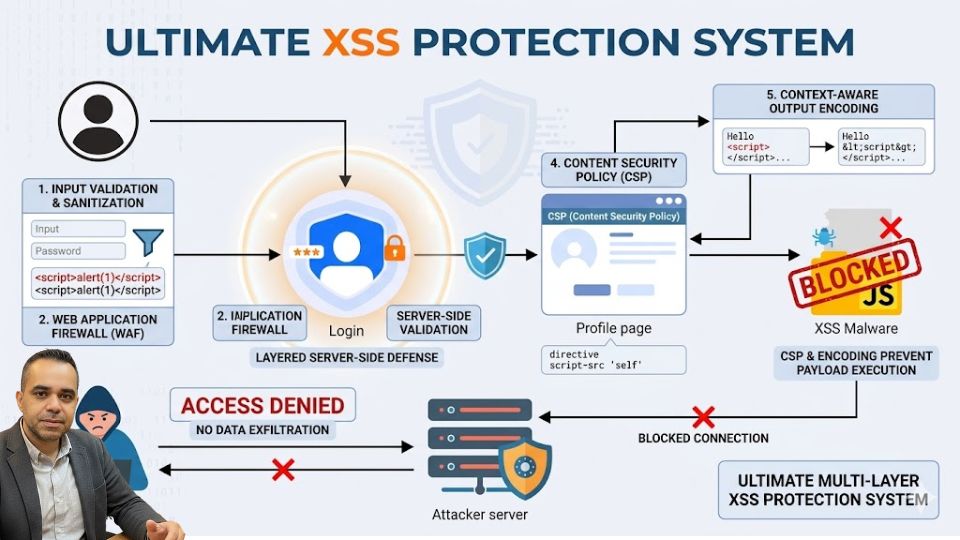
The Ultimate XSS Protection Guide: What Every Web Developer Must Know What Is Cross-Site Scripting (XSS)?
Cross-Site Scripting, commonly known as XSS, is one of the most prevalent and dangerous vulnerabilities in modern web applications. It occurs when untrusted user data is processed by a web application without proper validation and is then reflected back to the browser without encoding or escaping. The result is...
Read more: XSS Protection for Developers: A Complete Guide to...
Related Articles

